Rapidly Evolving and Increasing Cyberthreats: Why You Need an IT Assurance Service Program

The nature of business leans toward trying to operationalize the swiftest, most cost-effective solution to solve problems. Technology is often thrown at a problem without realizing the enormous cost of time and effort to implement it. Amid current information security risks and vulnerabilities though, cyber threat prevention and response activities need to be a fundamental component to every technology purchase, every system implementation, and every new integration point introduced. End users must be regularly educated about risks and understand their responsibility in protecting the organization from cybercriminals. A programmatic approach is critical, and strong coordination between business owners and IT is paramount.
Building an IT Service Assurance Program that ties your business and IT strategies – and the execution of those strategies – together can ensure your processes and workflows are enabled in a secure and resilient manner.
Understanding the Threat – and the Consequences
Health delivery organizations often develop business strategies and execution plans independently from IT, creating inconsistency and a lack of coordination. In the current climate, this inconsistency and lack of coordination can pose genuine information security risks with tangible financial costs and serious patient safety implications.
The last year alone has dramatically underscored the impact of rapidly evolving cyber threats – and information security vulnerabilities – in healthcare. Many health delivery organizations still lack even basic visibility into the medical devices (and other connected devices) they own, let alone understanding which of those might be at risk. Repeat ransomware attacks aimed at hospitals and health systems are increasingly common. Cyber insurance premiums are rising, and cyber policies now have more coverage exclusions. Meanwhile, new attack vectors and vulnerabilities continue to emerge (i.e., APIs) that hospitals and health systems need to be prepared to address.
The scope of cyber threats is also expanding. The reality is that cybercriminals are not just trying to infiltrate hospitals and health systems directly; they are also gaining access to health delivery organizations by targeting providers’ business and trading partners. Complicating matters is the increasing consolidation among third-party IT vendors, inconsistent due diligence from third-party vendors in vetting their own vulnerabilities, and misconceptions among vendors and providers alike about what is ultimately still a shared cloud security model.
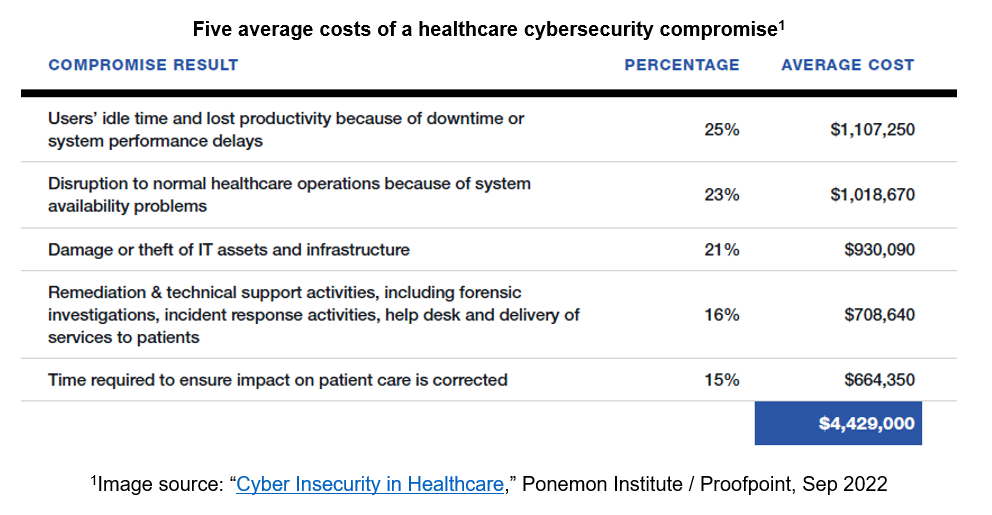
The consequences of experiencing a cyber-attack are significant and well-documented. There is a fundamental risk to patient safety if providers are unable to access key clinical applications. There are also direct and tangible financial costs – which go far beyond just paying the ransom. Additionally, it is impossible to put a price on a hospital’s reputation or the loss of public trust, and it can take years to recover from one bad headline about a breach or ransomware attack.
Why You Need an IT Service Assurance Program
Given the rapidly evolving and increasingly sophisticated information security risks that hospitals and health systems are facing – and the significant financial, patient safety, and reputational consequences that result from a cyber-attack – close coordination between business owners and IT is essential. Successful business execution is simply not possible without proactively accounting for current and emerging information security risks. IT needs to enable business priorities in a thoughtful and meaningful way, serving as a good business steward while also supporting the business with proper programs to ensure information security and resiliency. However, the only way an execution plan can be truly in synch between business owners and IT is if the strategy work is done collaboratively.
An IT Service Assurance Program is a foundation encompassing information security, business continuity, and disaster recovery that, once established, ties your business and IT strategies – and the execution of those strategies – together.
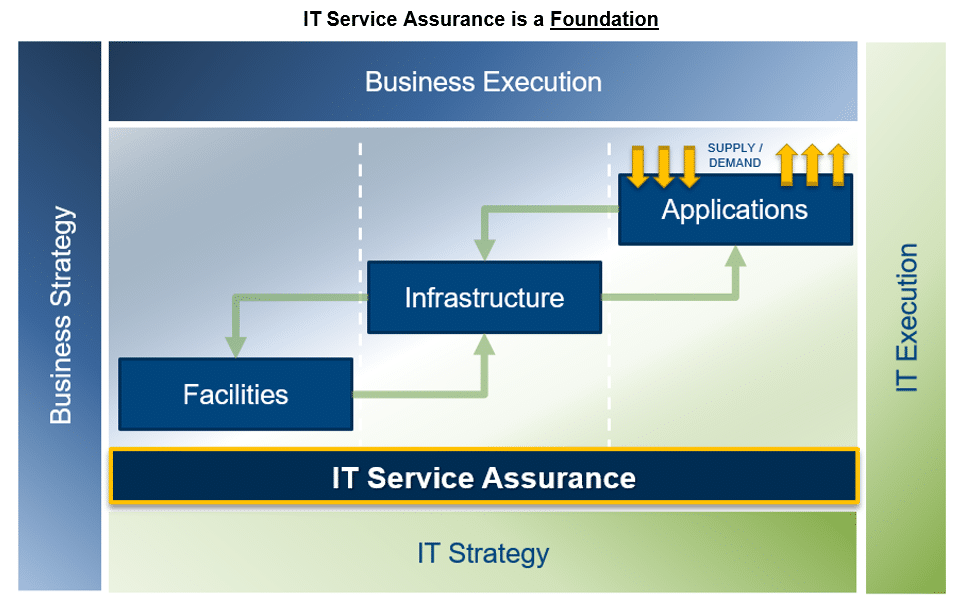
When properly governed (i.e., defined ownership of the process including roles and responsibilities, how handoffs are managed, etc.), an IT Service Assurance Program eliminates gaps in communication between business owners and IT, ensures adherence to agreed-upon information security standards across the enterprise, and promotes a culture of compliance, collaboration, and continuous improvement.
Under a well-governed IT Service Assurance Program:
- Your organization’s business strategies and IT strategies are developed in concert.
- Information security, disaster recovery, and business continuity are all approached proactively and programmatically across the enterprise.
- There is alignment between what your organization can reasonably deliver, support, and protect – and the technology that is purchased and implemented.
- Policies and procedures related to cyber threat prevention and response are well-defined, standardized, aligned with business priorities, and actively communicated across all levels of your organization.
- Your staff are well-prepared and regularly trained to recognize social engineering, phishing, vishing, and other attacks.
- Regular, comprehensive, and objective evaluations of your organization’s standards (policy, procedure, governance) are conducted to assess overall maturity and the measures needed to prepare for and respond to risk.
- Your business partners, third party vendors, and device makers are carefully evaluated. Your organization holds them accountable to the same standards and you align with those that have appropriate security controls.
- A business impact analysis is conducted to determine an intolerable amount of risk for your organization. Then IT security spending is aligned accordingly.
- Perhaps most importantly, your organization maintains the IT Service Assurance foundation that supports your people and your processes.
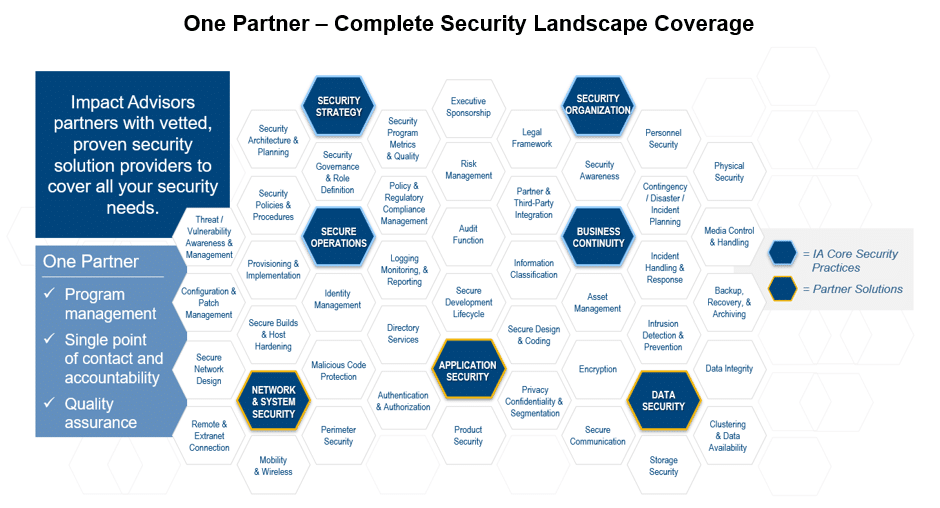
How Impact Advisors Can Help
Our team of healthcare security experts can help your organization improve compliance, identify risks, develop remediation plans, benchmark security posture, and track maturity improvement. We provide complete coverage of your security needs amid a complex landscape. Impact Advisors received Best in KLAS® for Security & Privacy Consulting Services for three years in a row – 2021, 2022, and 2023.